Methodology
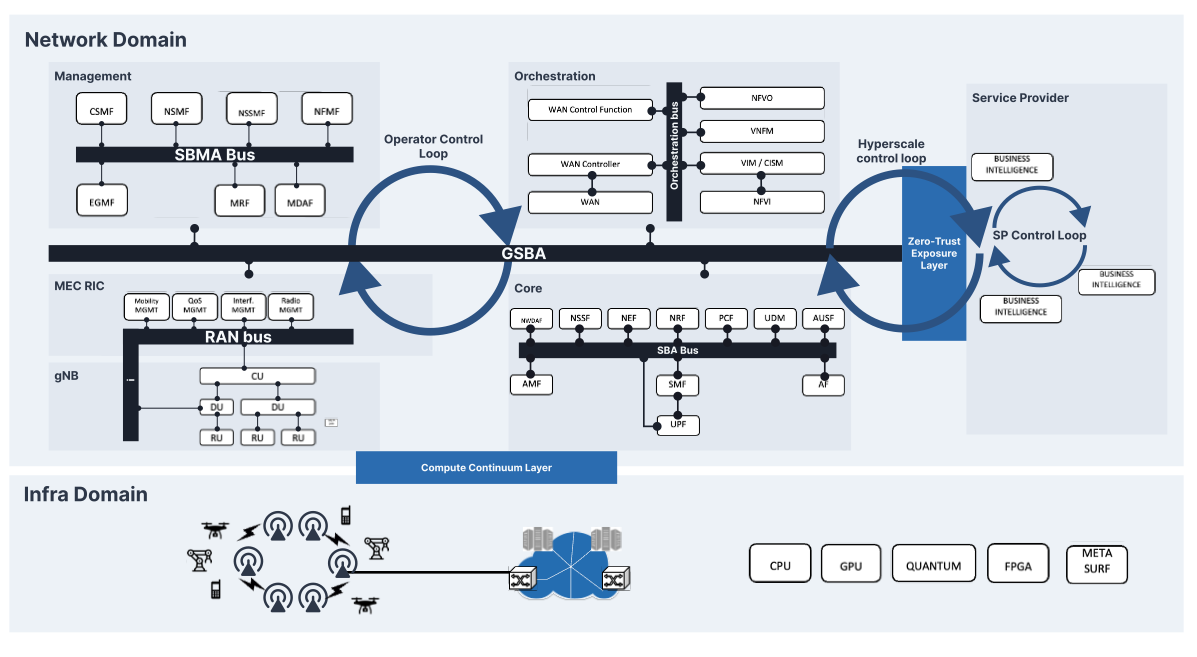
ORIGAMI proposes a methodology based on three architectural innovations that enable three global control loops that will support different Network Intelligence (NI) functionalities and global services. The three envisioned architectural enablers will evolve the network architecture beyond the current 5G SBA approach, effectively tearing down these barriers. This re-design, while maintaining the essence of the 5G architectural work, transitions into 6G by integrating the ORIGAMI architectural evolutions.
The Compute Continuum Layer (CCL)
ORIGAMI’s Compute Continuum Layer (CCL) is an innovative architectural component for 6G systems, envisioned to optimize network operations according to characteristics of the underlying infrastructure. The CCL will enable efficient resource sharing and will unlock the potential of heterogeneous computing infrastructures across multiple domains. It will support a variety of computing resources, including GPUs, TPUs, FPGAs, ASICs, NPUs, smartNICs, and even novel quantum computing paradigms, accelerating Virtual Network Functions (VNFs) and complementing conventional CPUs.
The Zero-Trust Exposure Layer (ZTL)
The ZTL enables the matching between the internal operation of the service provider's business logic and the network operator's continuous optimization. This cooperative control loop can unleash all the potential of the network deployment by (i) having a more direct influence on the operation internals and (ii) unlocking beyond data-transfer functionality such as remote sensing or digital twinning directly to the providers. Thanks to this view, ORIGAMI aims to provide verticals with network hyperscalers in a similar way computing hyperscalers (such as Amazon AWS, Microsoft Azure, and Google Cloud Services) are already providing for other purposes.
The Global SBA (GSBA)
Both ORIGAMI ́s CCL and the ZTL (together with the other legacy domain buses, such as 3GPP SBA) rely upon the Global SBA (GSBA), which is meant to enable the declaration and management of services between different domains (e.g., network operators, and infrastructure providers). In our vision, a “domain” maps to an entity that owns different sub-domains, such as the radio access network, the core network, and the international carrier network. Within this ecosystem, one of the major challenges we aim to tackle is the inherent lack of trust between the different entities, which makes resource sharing and the deployment of novel business models difficult.
The architectural innovations brought by GSBA, CCL, and ZTL pave the way to new control loops in the mobile network operation:
- The Operator Control Loop expands upon existing control loops available per domain, such as those in the RAN domain between the RIC and other elements of the O-RAN architecture, or the loop created by the NWDAF in the core domain. This expansion aims to achieve a holistic view of network resources. The GSBA will effectively integrate the currently scattered and siloed domains into a unified fabric, where all intelligent algorithms can coexist and cooperate for the optimal operation of the network, adhering to Network Operator policies.
- The Hyperscale Control Loop offers new opportunities for both Service Providers and Network Operators, and is enabled by the ZTL and the GSBA, which serves as a gateway for more flexible interactions between those actors. Specifically, Service Providers can enjoy a broader range of exposed network capabilities, leading to seamless customization, while Network Operators can diversify their service portfolio based not only on service types (e.g., eMBB or URLLC) and associated KPIs, but also on the available customization capabilities. By employing tiered pricing models used by Software-as-a-Service (SaaS) companies, Network Operators can monetize various levels of functionality and cater to a wider range of customers.
Through these loops, ORIGAMI will enable the designing and development of innovative network architectural extensions that ensure synergistic operation and address the challenges mentioned earlier. These three architectural innovations will be utilized by specific Network Intelligence (NI) algorithms that capitalize on the newly created closed loops. To effectively enable this vision, a number of NI functionalities and services will exploit these closed loops, on top of ORIGAMI’s architectural innovations:
- NI realizing more efficient vRAN approaches that reduces costs without sacrificing reliability through pooling computing infrastructure and opportunistically offloading signal processing tasks to the best available computing resources.
- NI implementing scalable and generalizable ML models for network management, focusing on anomaly detection and leveraging ORIGAMI’s architectural innovations to enhance data collection, ultimately improving interoperability and facilitating the deployment of a RAN bus and RIC in Open RAN architectures.
- NI supporting a network control and management via employs scalable and robust online learning algorithms, deep-learning-based optimization at (sub)msec granularity, data- efficient Bayesian learning methods, and quantum computing-assisted optimization techniques such as quantum annealing and quantum approximate optimization.
- NI allowing operators and tenants to transparently exploit the in-band computing capabilities of modern programmable transport domains, and enabling an effortless deployment of 6G VNFs into the user plane of the communication network transport domain.
- NI realizing a DLT-based solution for making resource awareness global, and allowing dynamic business models to take shape, so as to deliver a new kind of trust to a wide range of services, including the largely opaque cellular roaming ecosystem.
- NI supporting a common data representation for network monitoring feeds and implementing proactive solutions for network troubleshooting.
- NI enabling a Service Communication Proxy (SCP)-enabled 6G network core as a fully service-mesh, utilizing ML techniques and graph theory to model, analyze, and optimize traffic flows and network core signaling.